LondonCD meetup group on 12 June 2017. The other posts are linked at the end of this article.
Applying the principles and practices of Continuous Delivery for new software is fairly straightforward (at least, until you deal with data and databases). However, existing “legacy” systems that were built without many automated tests and without much concern for repeatable deployments of discrete functionality pose a challenge for moving to Continuous Delivery.

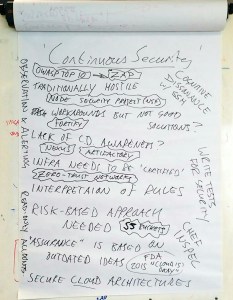
Continue reading Continuous Delivery for Legacy/Heritage Systems – LondonCD meetup June 2017